OneHoster’s Services Includes
OneHoster has a stable structure for web hosting, web design, web development, digital marketing and graphic design. Our services have been recognized internationally through providing real services for our clients all over the world and independent end users.
OneHoster will offer you the effective online marketing to get more potential customers, we have a digital marketing strategy built on the idea of rapid growth, using innovative, scalable and cost-effective digital marketing technologies that make them suitable for all business categories.
Our Services Include
Web Hosting and Web Solutions:
- Domain Name registration.
- Web Hosting.
- Web Design and Web Development.
- E-Commerce Solutions.
- Digital Marketing Solutions.
- Search Engine Optimization (SEO).
- Customizable Web Applications such as Photo Albums, Discussion Forums, Helpdesk systems and Application Localization.
Graphic Design and Printing:
- Corporate identity and image building.
- Graphic design (Logo design, stationery design, promotional materials, banners design and exhibition tools).
- Marketing, promotion and advertising solutions.
- Events Services.
- News papers and magazine ads.
- Packing design (labels, bags, boxes and stickers).
- Software and applications design.
- Illustration.
- Annual reports design and printing.
- Offset printing and Digital printing (outdoor -indoor).
Digital Marketing:
- SEO (Search Engine Optimization).
- Social Media Advertising.
- Email Marketing.
- SEM (Search Engine Marketing).
- Content Marketing.
- Website Design & Development.
Multimedia and Photo shooting:
- Promotional Multimedia CDs.
- Video presentations.
- Professional photo shooting.
- Image modifications and editing.
What are you waiting?
Grow your business, get more customers and beat your competition!
We offer many marketing tools and advertising services for all clients in Egypt and Middle East. Increase your sales with OneHoster “your partner in success”.
Click here and contact OneHoster, and we will respond to you with a proposal within 24 hours:
OneHoster is one of the best web hosting companies in Egypt, we offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses. OneHoster is also one of the top 10 website design companies, and top 10 digital marketing companies in Egypt and Middle east.
“OneHoster’s Team”
How to Choose Best Web Hosting Provider, Tips for Choosing the Best Web Hosting Company, to Get The Best Web Hosting for Small Business or Medium Business
Business owners understand the value of creating good web content and they are finally beginning to understand the importance of developing a web site that is responsive for mobile users. But most of them ignore the importance of selecting a reliable web hosting company. When business owners take the time to select a reliable web hosting company, they ensure their website remains accessible and safe at all times. choosing a web host, based on something like pricing only, can produce disastrous results.
Choosing the best web host for your website can be a confusing process and not one you should take lightly. There are some important factors you should consider when choosing a web host. OneHoster.com will give you some tips for choosing the best web host, from researching speed and reliability to exploring security features.
Did you think what will happen if your website will down, when your website is down, it’s like having the door locked and the closed sign hanging at a brick-and-mortar business. Your customers can not enter your store to shop and you can not make money.
Websites are designed to allow customers to shop 24 hours a day. This doesn’t happen if your website is inaccessible. In August 2013, Amazon lost $66,240 per minute when the web site went down for more than 30 minutes.
How to avoid problems with your web host
Here are some tips that will help you choose the right web host, and avoid mistakes that can create big problems later.
- Know what kind of web hosting is needed: understanding the needs of your business can help narrow your web hosting options. Websites that receive a lot of daily traffic will likely not function well on a shared server because these servers are designed to accommodate a lot of small websites that have limited demands. If you plan to build a website that features video blogging, 24-hour live streaming and the ability for visitors to register and upload their own videos, your website would require more features than someone who just uses their website as a virtual resume.
- Avoid the new companies that can not handle growth: many new companies offer low prices hoping they will make up for it with a large influx of clients, when web hosting companies experience growth too quickly and they don’t have the resources to handle it, that creates problems for business owners like downtime, slow page loads, lost revenue, and negative effects on search rankings, most new hosting companies are not equipped to successfully manage that many clients at once. It’s best to stick with a more established company that can deal with growth without compromising their clients’ experience.
- Is there a backup plan: It doesn’t really matter why your website is down or why you have lost your website’s data, you need to know if the web hosting company you choose has a backup plan to help you recover just in case.
- Ask about security features: security breaches happen, make sure your web hosting company can provide secure sockets layer to safeguard your customer’s private information. This is an essential feature in providing customers with safe transactions and it should be a feature that’s provided by the web hosting company.
- Customer support: when you are researching web hosting companies, always look for a way to contact customer support. Can you find a quick and easy way to contact them via email, online chat, or 24/7 phone support?
- Don’t get stuck on price: when you are a new business owner with a limited budget, the web hosting company offering the lowest price might be very tempting, remember you get what you pay for. The cheapest price might just result in slow servers, poor customer service, constant downtime, and an association with thousands of unprofessional websites.
- How much traffic do you expect to receive each month? Be realistic, this will help determine how much resources you need, if you plan to grow your traffic over time, you may need a host that offers salability in their package offerings.
- What type of site will you be creating? for example, will you be working with WordPress or creating a static HTML website?
- What technical requirements will you require for your website? most coding languages like HTML and CSS don not have special requirements, but if you’re working with PHP, for example, you’ll need to find a host who can cater to that language.
- Do you need extra features: such as email hosting or an SSL certificate, be sure the host you choose offers what you’re looking for and at a reasonable rate.
- Is there SSD drives for all plans? For more speed web hosting companies use solid-state drives on all web hosting plans.
- Does they offer free SSL certificate? most web hosting companies provide Free Let’s Encrypt SSL certificate with each account.
- Own firewall security rules: does the web hosting company has wrote WAF rules to fix zero day vulnerabilities.
- Quality hardware: infrastructure components are Datacenter Grade designed.
- Type of control panel: is there a cpanel support, most web hosting companies offer cpanel with all plans, but some others not, be sure that this web hosting support cpanel web hosting.
Finally, be sure to look at the web hosting that is good for you, be sure also if the web hosting company will offer you add-ons and extra services or not, some hosts for example, does not give you extra email hosting, extra disk space. There’s a lot to consider when choosing a web host, and it all starts with knowing what your needs are so you can find the host best suited to you.
OneHoster is one of the best web hosting companies in Egypt, we offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses. OneHoster is also one of the top 10 website design companies, and top 10 digital marketing companies in Egypt and Middle east.
“OneHoster’s Team”
Mobile Web Best Practices
Developing a mobile web site could be not a hard task if you know what device you talk with and its screen size and use the best XHTML code it will be very easy to do it, the real problem comes when you want to ensure that its work well across different devices, adaptation sure help in this task but if you follow some check list it will give us best results.
Best Practices in delivering web content to mobile devices. The principal objective is to improve the user experience of the Web when accessed from such devices, there is much computation in the web to provide us with the best practice for creating a good mobile web site, and here is a list for some of them:
- W3C mobile best practices (http://www.w3.org/TR/mobile-bp)
- Luca Passani Global Authoring Practices for the Mobile Web (http://www.passani.it/gap)
- Making Small Devices Look Great (http://dev.opera.com/articles/view/making-small-devices-look-great)
- Best Practices in XHTML Design (http://developer.openwave.com/dvl/support/documentation/guides_and_references/best_practices_in_xhtml_design/index.htm)
- As W3C is the responsible organization to develop common standards for the World Wide Web so we will list some of mobile Web best practices that W3C tell us about.
- Ensure that content provided by accessing a URI yields a thematically coherent experience when accessed from different devices.
- Exploit device capabilities to provide an enhanced user experience.
- Take reasonable steps to work around deficient implementations.
- Carry out testing on actual devices as well as emulators.
- Keep the URIs of site entry points short.
- Provide only minimal navigation at the top of the page.
- Take into account the trade-off between having too many links on a page and asking the user to follow too many links to reach what they are looking for.
- Provide consistent navigation mechanisms.
- Assign access keys to links in navigational menus and frequently accessed functionality.
- Clearly identify the target of each link.
- Note the target file’s format unless you know the device supports it.
- Do not use image maps unless you know the device supports them effectively.
- Do not cause pop-ups or other windows to appear and do not change the current window without informing the user.
- Do not create periodically auto-refreshing pages, unless you have informed the user and provided a means of stopping it.
- Do not use markup to redirect pages automatically. Instead, configure the server to perform redirects by means of HTTP 3xx codes.
- Keep the number of externally linked resources to a minimum.
- Ensure that content is suitable for use in a mobile context.
- Use clear and simple language.
- Limit content to what the user has requested.
- Divide pages into usable but limited size portions.
- Ensure that the overall size of page is appropriate to the memory limitations of the device.
- Limit scrolling to one direction, unless secondary scrolling cannot be avoided.
- Ensure that material that is central to the meaning of the page precedes material that is not.
- Do not use graphics for spacing.
- Do not use images that cannot be rendered by the device. Avoid large or high resolution images except where critical information would otherwise be lost.
- Ensure that information conveyed with color is also available without color.
- Ensure that foreground and background color combinations provide sufficient contrast.
- When using background images make sure that content remains readable on the device.
- Provide a short but descriptive page title.
- Do not use frames.
- Use features of the markup language to indicate logical document structure.
- Do not use tables unless the device is known to support them.
- Do not use nested tables.
- Do not use tables for layout.
- Where possible, use an alternative to tabular presentation.
- Provide a text equivalent for every non-text element.
- Do not rely on embedded objects or script.
- Specify the size of images in markup, if they have an intrinsic size.
- Resize images at the server, if they have an intrinsic size.
- Create documents that validate to published formal grammars.
- Do not use pixel measures and do not use absolute units in markup language attribute values and style sheet property values.
- Use style sheets to control layout and presentation, unless the device is known not to support them.
- Organize documents so that if necessary they may be read without style sheets.
- Keep style sheets small.
- Use terse, efficient markup.
- Send content in a format that is known to be supported by the device.
- Where possible, send content in a preferred format.
- Ensure that content is encoded using a character encoding that is known to be supported by the target device.
- Indicate in the response the character encoding being used.
- Provide informative error messages and a means of navigating away from an error message back to useful information.
- Do not rely on cookies being available.
- Provide caching information in HTTP responses.
- Do not rely on support of font related styling.
- Keep the number of keystrokes to a minimum.
- Avoid free text entry where possible.
- Provide pre-selected default values where possible.
- Specify a default text entry mode, language and/or input format, if the target device is known to support it.
- Create a logical order through links, form controls and objects.
- Label all form controls appropriately and explicitly associate labels with form controls.
- Position labels so they lay out properly in relation to the form controls they refer to.
OneHoster offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses.
“OneHoster’s Team”
Cloud Computing
Cloud Computing is the latest paradigm that involves delivering hosted services over the Internet. Everyone linked with the cloud industry has his own definition. Users of cloud computing can access applications and documents from anywhere in the world the same way as with desktop computers and making it easier for group members in different locations to collaborate. In cloud computing, everything is hosted in the cloud network which is a collection of computers and servers accessed via the Internet. The history of cloud computing is coming from the electricity revolution, a century ago. Before the advent of electrical utilities, every farm and business produced its own electricity from freestanding generators. After the electrical grid was created, farms and businesses shut down their generators and bought electricity from the utilities at a much lower price and with much greater reliability than producing it. Universal access and 24/7 reliability are guaranteed while ubiquitous collaboration is.
Now cloud industry is currently in the early days of the cloud computing revolution. As Sun Microsystems’s slogan is “The network is the computer”, and that’s as good as any to describe how cloud computing works. In essence, a network of computers functions as a single computer to serve data and applications to users over the Internet. The network exists in the cloud of IP addresses that is known as the Internet, offers massive computing power and storage capability, and enables wide scale group collaboration. The definition of the cloud is it is a large group of interconnected computers. These computers can be personal computers or network servers and can be public or private.
OneHoster offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses.
“OneHoster’s Team”
The Two Extremes of Mobile Applications
The foundation for a new era of computing model, which is called mobile cloud computing, comes from the combination of cloud computing, portable computing devices, wireless communication, location based services, mobile Web, etc.. The mobile devices allow the users to access an unlimited computing power and storage space within the mobile domain. There are many hurdles to overcome in mobile cloud computing. The existing cloud computing tools tackle only specific problems such as flexible virtual machine, managing parallelized processing on massive data volumes, and large data storage.
Mobile devices inherently have and will continue to have limited resources as processing power, memory capacity, display size, and input forms. These have been the forming factors of existing mobile application approaches. This is why mobile computing is characterized by severe resources constraints and frequent changes in operating conditions. To identify the fundamental challenges in mobile computing, many research are done in this area. The full potential of mobile cloud applications lies in between the following two extremes:
1. Mobile clouds native applications (offline applications)
This is the first model that most of the applications available for modern mobile devices fall into, which is often called “native applications”. The periodical synchronization between the client and backend system is the main issue here. This model acts as a fat client because the processing of the presentation and business logic layer is locally done on the mobile devices, while the data is downloaded from the backend system. Most resources are available locally on the fat client, rather than distributed over a network as is the case with a thin client. As with everything in computer world there are advantages and disadvantages, below are some of them.
Offline applications advantages:
- Have a good integration with device functionality.
- A full access to device features.
- Have a great performance optimized for specific hardware or multitasking.
- Even if there is no network connectivity, always have available capabilities.
Offline applications disadvantages:
- No portability to other platforms.
- Complex coding.
- Increased time to market.
- Developers need to learn new programming languages.
2.Web applications (online applications)
This application model requires that the connection between the mobile devices and the backend systems are available most of the time. This application type is based on the Web technology that is a powerful alternative to native applications in which the cross platform issues are solved. The advantages of this model overcome some of the disadvantages of the offline applications, but it also has some disadvantage.
Online applications advantages:
- Considered as multi platforms.
- Directly accessible from anywhere any time whenever there is connection.
- The learning curve required to start creating mobile applications is greatly minimized, because the knowledge of most Web technologies is currently widespread among developers.
Online applications disadvantages:
- Too much introduced latency for real time responsiveness.
- Device’s features access is limited such as camera or motion detection.
- Difficulties in handling complex scenarios that require keeping communication session for long period of time.
When accessing remote data and services, mobile clients could face problems like, wide variations, rapid changes in network conditions and local resource availability. The execution of current applications could be partitioned to happen on the device or on backend systems, because of this statically partitioned one partitioning model does not satisfy all application types and devices. The computation of clients and cloud has to be adaptive in response to the changes in mobile environments. Mobile cloud applications must react with dynamical adjusting of the computing functionality between the mobile device and the cloud depending on circumstances, in order to enable applications and systems to continue to operate in such dynamic environments.
Many researchers work on how could dynamically shift the responsibilities between mobile device and cloud. Some shown how to achieve that is by replicating whole device software image or offloading parts of the application, so the offloading can happen to some remote data center, nearby computer or cluster of computers, or even to nearby mobile devices, due to the unstable mobile environments. Many factors need to be incorporated in a cost model, and fast predictive optimizing algorithms decide upon the best application execution, thus for many years to come mobile cloud computing will become challenging research area.
OneHoster is one of the best web hosting companies in Egypt, we offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses. OneHoster is also one of the top 10 website design companies, and top 10 digital marketing companies in Egypt and Middle east.
“OneHoster’s Team”
Cloud Architecture
A massive network of servers or even individual PCs interconnected in a grid is the key of cloud computing. These computers run in parallel, combining the resources of each to generate super computing power. One of the primary benefits of cloud computing is a vast amount of computing power achieved from relatively low cost PCs and servers.
The collection of computers and servers that is publicly accessible via the Internet creates the cloud. This hardware is typically owned and operated by a third party on a consolidated basis in one or more data center locations. The machines can run any combination of operating systems. Cloud architecture is deceptively simple, although it does require some intelligent management to connect all those computers together and assign task processing to multitudes of users.
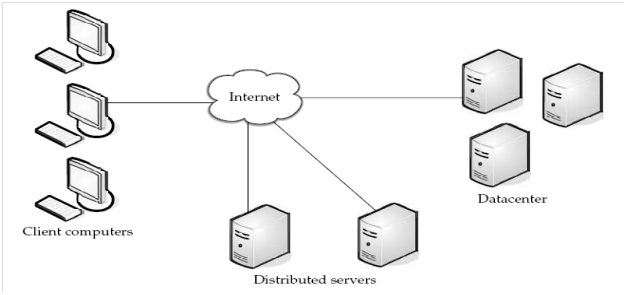
One of the primary uses of cloud computing is for data storage in which data is stored on multiple third party servers rather than on the dedicated servers used in traditional networked data storage. When storing data, the user sees a virtual server and it appears as if the data is stored in a particular place with a specific name. The place does not exist actually and it is just a nickname that is used to reference the virtual space from the cloud. The users data could be stored on any one or more of the computers used to create the cloud, as the cloud dynamically manage available storage space. But even though the location is virtual, the user sees a static location for the data and can actually manages the storage space as if it resides in his own PC. In addition, multiple copies of the same data are stored in the cloud servers. The duplication of the data are kept continually; so the cloud continues to function as normal even if one or more servers go offline or even crashes. Cloud computing solutions are made up of several elements, the clients, the data center, and the distributed servers, as illustrated by Figure 1.1.
- The client’s component
Is the first of the cloud components, and it could be described as the devices that the end users interact with to manage their information on the cloud. Clients are the exact same things that they are in the traditional computing. Clients fall into three main categories:
- Mobile devices which include PDAs or smart phones, like a Blackberry or an iPhone,
- Thin clients which are computers that do not have internal storage, but rather let the server do all the work then just display the information, and
- Thick clients which are regular computers using a Web browser like Firefox or Internet Explorer to connect to the cloud.
- The data center component
These are the collection of web hosting servers where the application to which the user subscribe is hosted. It could be a large room in the basement of a building or a room full of servers on the other side of the world that the user can access via the Internet. A growing trend in the IT world is software that can be installed allowing multiple instances of virtual servers to be used called virtualization servers.
- Distributed Servers
These servers don’t have to be housed in the same location, these servers are hosted in geographically different locations, and the cloud subscriber does even see that. These servers act as if they are single group right next to each other. This gives the service provider more flexibility in options and security. For instance, Amazon has their cloud solution in servers all over the world. If something were to happen at one site, causing a failure, the service would still be accessed through another site. Also, if the cloud needs more hardware, they need not throw more servers in the safe room they can add them at another site and simply make it part of the cloud.
OneHoster is one of the best web hosting companies in Egypt, we offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses. OneHoster is also one of the top 10 website design companies, and top 10 digital marketing companies in Egypt and Middle east.
“OneHoster’s Team”
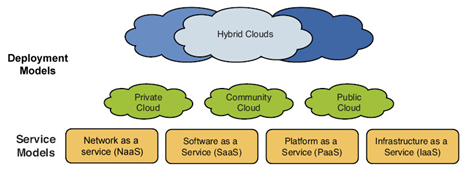
Cloud Deployment Approaches
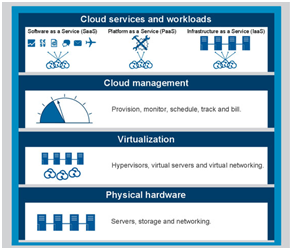
Cloud computing services are offered through some cloud deployment approaches. Cloud deployment service can be classified into four main types, public, private, community, or hybrid. Cloud framework begins with the physical hardware of the cloud. The virtualization layer comes above the hardware layer, the next layer is the cloud management layer, and the final layer is the cloud services layer which is deployed by the cloud providers to make the cloud provisions available to the cloud consumers such as IaaS, PaaS and SaaS. Figure 1.1 illustrates this concept.
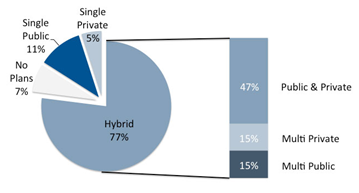
Cloud deployment models used to power the organization to provide services to its customers, choosing the deployment model is one of the biggest challenges that face any organization. One of the most common strategies is the public cloud services for development and test or less critical applications, allocating business critical applications to a more enterprise class cloud and running their mission critical apps on an in house cloud. Following is a discussion of the deployment types. Figure 1.2 illustrates the current percentage for each of these types.
Private Clouds
When there is an internal data centers of a business or organization and is not made available for the public, it is called a private cloud. Sometimes private cloud named as an internal cloud and this type of cloud exists within the boundaries of an organization. Private cloud is a computing platform or architecture that provides hosted services to a limited number of people behind a firewall. The infrastructure for private cloud is operated solely for a single organization, but it managed internally by a third-party that hosted internally or externally. The virtualization and distributed computing is required to setup a private cloud project, this makes the organization reevaluate decisions about existing resources. Organizations should buy, build, and manage the hardware and software by themselves.
Private cloud is designed to offer the same features and benefits of public cloud systems, but removes a number of objections to the cloud computing model including control over enterprise and customer data due to worries about security and issues connected to regulatory compliance. Because a private cloud setup is implemented safely within the corporate firewall, the implementation is aimed to avoid many of the objections regarding cloud computing security. A private cloud provides more control over the company’s data and ensures security, albeit with greater potential risk for data loss due to natural disaster. When an organization implements the private cloud, it is responsible for running and managing the IT resources instead of passing this responsibility on to a third-party cloud provider.
Public Clouds
Public cloud is a computing environment that consists of a set of computers and computer network resources based on the standard cloud computing model that is open for use to the public. Public cloud is a cloud services provided by third parties but hosted and managed by the service providers. The infrastructure is owned by an organization that sale the cloud services to the general public or to a large industry group. Using public cloud, users could delegate all service management and support to the service provider who is taking the responsibility of installation, management, provisioning, and maintenance. Applications, storage, and other resources are made available to the general public by the service provider. Public cloud customers only access and use the services and physical resources and they are charged for the used resources and services only.
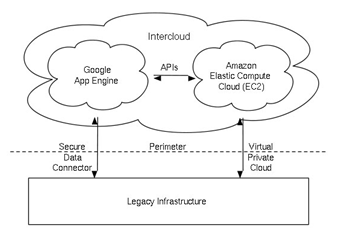
There is a special type of deployment model called Virtual Private Cloud (VPC) that comes to exist when the service provider uses public cloud resources to develop a private cloud environment. Users can create a VPC as configurable pool of shared computing resources allocated within a public cloud environment. Figure 1.3 illustrates the way to create virtual private cloud. The cloud provider usually choose the hardware and the cloud users cannot do this like in the private cloud. The virtualization and device independence is very clear in this type, so the public cloud can be described as an external cloud when viewed from within a given organization.
Community clouds
When sharing infrastructure between several sites and organizations with common issues such as security, compliance, etc., this is called a community cloud. It is hosted internally or externally and could be managed internally or by a third party. The cost is spread over fewer users than a public cloud, only some of the cost savings potential of cloud computing are realized. Community cloud is best when looking for energy, cost efficiency, and vertical applications. Any software that support specific business processes to targets a smaller number of users within an organization called a vertical application. Enterprise Resource Planning (ERP) and Customer Relationship Management (CRM) are examples of vertical applications.
All kinds of underutilized and unutilized computing machines are being networked, clustered, and virtualized to act as a community cloud that is capable of effortlessly to tackle specific needs of a particular community. Community cloud offers an alternative architecture for the use cases of cloud computing. The community cloud is not owned or controlled by one organization, and therefore not dependent on the lifespan or failure of any one organization. It is resilient to failure and robust, with no system wide cascade failures, because of the diversity of its supporting nodes. Community cloud offer control convenience because its community ownership provides for democratic distributed control. Community cloud makes use of underutilized user machines that require much less energy than the dedicated data centers required for vendor Clouds.
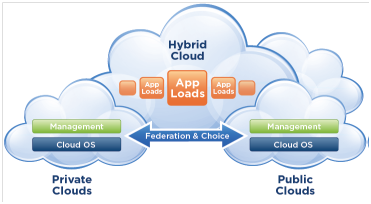
Hybrid Clouds Enterprises
The combination of private, community, and/or public clouds are called hybrid clouds. This composition of two or more clouds offers the benefits of multiple deployment models. This type of composition expands deployment for could services and allow organizations to use public cloud resources to meet temporary needs. This allows hybrid cloud to enable cloud bursting for scaling across clouds. The common big misperception is that cloud computing implies an external cloud, based on public cloud services. But the fact is that cloud computing is how to approach information technology. It is a way of doing computing, not a destination. Most enterprises will benefit from adopting cloud computing within their own data centers building which is a private clouds, and getting there in an evolutionary way through their existing virtualization technology. Figure 1.4 illustrates how hybrid cloud infrastructure works.
Cloud bursting is an application deployment model in which an application runs in a private cloud or data center and bursts to a public cloud when the demand for computing capacity increases. Primary advantage of cloud bursting and a hybrid cloud model is that an organization only pays for extra compute resources when needed. Cloud bursting enables data centers to create an in house IT infrastructure that supports average workloads and use cloud resources from public or private clouds during spikes in processing demands. A high degree of fault tolerance combined with locally immediate usability is obtained when using hybrid cloud architecture without depending on Internet connectivity. Hybrid cloud architecture requires both on premises resources and off site or remote server based cloud infrastructure. Hybrid cloud provides the flexibility of in house applications with the fault tolerance and scalability of cloud based services.
OneHoster is one of the best web hosting companies in Egypt, we offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses. OneHoster is also one of the top 10 website design companies, and top 10 digital marketing companies in Egypt and Middle east.
“OneHoster’s Team”
Evolution of the Internet
The Internet is far more than just the World Wide Web. The Web was created in 1989 and became popular in the 1990s. In contrast, the Internet is a product of the1960s. The Internet is a vast network of networks that electronically connects millions of people worldwide. It was formed in 1968, when the U.S. Department of Defense’s Advanced Research Projects Agency (ARPA) funded what would become the first global computer network, the Advanced Research Projects Agency Network (ARPANET). ARPA later became the Defense Advanced Research Projects Agency (DARPA). The ARPANET allowed university and government engineers to research and work from any location on the network. ARPANET’s design featured multiple hosts and multiple connections among those hosts, which greatly reduced the chances of total network failure. There was no central hub, which would have created a point of vulnerability; rather, control was spread throughout the network. This decentralization resulted in a robust and reliable network that would continue to function even if some of the hosts were incapacitated.
In 1989, the Department of Defense decommissioned the ARPANET, and all the sites switched over to the National Science Foundation (NSF) network, called NSFnet. The NSF increased the number of supercomputers to five and added access to more networks, expanding the range of sites for businesses, universities, and government and military installations. The NSFnet, plus thousands of others, compose what has become the largest network of networks: the Internet.
The World Wide Web if the most important concept to remember is that the Web is not a network itself, like the Internet, but a set of software programs. These programs can be used on many different computer networks, including the Internet and your company’s computer network, the Web presents information through multimedia formats: graphics, sound, animation, and video. It employs several tools to provide a visual layout: hypertext links, browser software, and code structure.
The Web resembles an electronic library, and therefore each location or Web site is like a book. Each book has a contents page that directs you to the other pages in the book, as well as to all the other books in the electronic library. At the beginning of the internet these books are created using the Hypertext Markup Language (HTML), after a while there was another technologies that embedded with HTMLs along with interactive objects such as Java, JavaScript and VBScript can add extensive functionality to Web pages.
As we see in this brief overview for the evolution of the internet and the web, we notice that the web was first design to just provide information that could be accessed from desktop computers, in the early days of the web there was no mobile devices and there was no need to access it from such devices, but now a days when the mobile technology run very fast and when mobile become an important part of our daily life here accessing the Internet from mobile devices is becoming increasingly popular. Web access from mobile devices presents its own unique challenges, Mobile web users face a big problem that the majority of web content is tailored for desktop computers; there were many trials to solve this problem. The principal objective is to improve the user experience of the web when accessed from such devices.
Researchers try to find solution to make mobile web users able to run the web from their devices but they face many problem and they have to solve them, there was many problems that is related to the hard ware of the mobile devices like small display area, lower processor memory and many other limitations that we will discuss, and there is also some software problems like each mobile device run its own operating system and its web browser also, here in this thesis we will focus on the problem of different screen size and how can we adopt the web site to match this verity of screens.
There was much researches that was done in this area, some of them focus on how can we have two versions of each web site one for the desktop users and other for a mobile users and how the mobile version should be, some others focus on create only one version and have a small module that re-author the original web to have a new version that could match the mobile users, also there was some peoples say that we don’t have to make another version to match mobile we can run the desktop version if we don’t have much users for this web site.
OneHoster is one of the best web hosting companies in Egypt, we offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses. OneHoster is also one of the top 10 website design companies, and top 10 digital marketing companies in Egypt and Middle east.
“OneHoster’s Team”
Overview About Mobile Devices
Today there are hundreds of mobile phones in the market; mobile phones are not the only mobile devices there are also pocket computer devices like PDAs, micro notebooks and handheld notebooks, here I will take about mobile phones, PDA and some other mobile devices.
Mobile Phones
The largest segment for mobile devices, they have specialty processor and there own operating system the widely used is Symbian or windows mobile but there is also others, At the first development of mobile phone its use was voice and text messages but the technology over the years go fast for other uses like play music, photos, run applications and many other options this change the use of mobile from simple feature phone to smart phone.
The standard input for mobile phones is a 12 keypad with additional function keys, some other have joystick that can be used in navigation, with wider screen models there was other style available like input through touch screen keyboard like iPhone, some others have a keyboard input like Nokia E61, 63 or 71. Today most of mobile phones come with web browser like opera mini which is the most popular web browser some other come with different types of browsers.
Personal Digital Assistants (PDA)
Personal Digital Assistants (PDA) is the other class of mobile devices, it contain many other business features and productivity applications like office and emails, the most important that it can have their custom software, they have QWERTY keyboard in the device or screen, phone function is add on for PDSs, this type of devices are very popular with business users and merging phone with the device itself.
Other Mobile Devices
Micro notebooks and handheld notebooks can be classified as a mobile device, technology expect many hybrid devices to come up in the next few years that will have higher computing power and mobile communication technology.
OneHoster is one of the best web hosting companies in Egypt, we offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses. OneHoster is also one of the top 10 website design companies, and top 10 digital marketing companies in Egypt and Middle east.
“OneHoster’s Team”
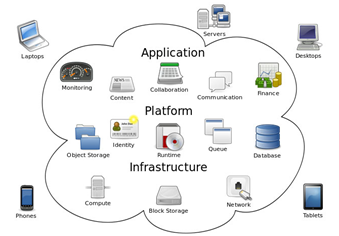
Cloud Service Model
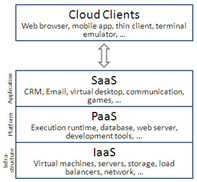
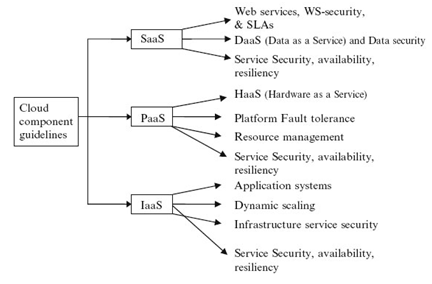
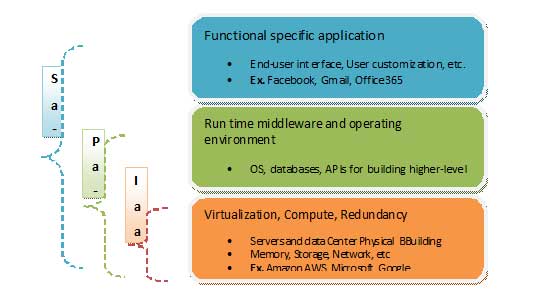
Cloud services are the basic principle behind the emergence of cloud computing. As explained earlier, there are generally four types of deployment approaches which are private clouds, public clouds, community clouds, and hybrid clouds. Meanwhile, there are three main categories of services that can be offered by any cloud architecture and technology. The first category is Infrastructure as a Service (IaaS) which is a concept of providing the whole IT infrastructures such as storage, virtual environment, servers, platforms, and applications. The second category is Platform as a Service (PaaS), which is a concept of providing a complete service level application development environment, as a service over the Internet right from requirements to the complete life cycle. Last category is Software as a Service (SaaS) which is a concept of providing software applications as a service on demand over the Internet that means it can be run anywhere and anytime. In addition to pay per use rather than to buy, Figure 1.1 illustrates the cloud services model overview.
Figure 1.2 illustrates the service models and the cloud deployment models. All the services can be delivered on any of the cloud delivery models, PaaS and SaaS is often used in conjunction with other software. When they are used as a component of another application, this is called a plug-in or mashup.
Infrastructure as a service (IaaS)
IaaS is simply the physical and virtual resources used to build the cloud. IaaS composed essentially from hardware devices like visualized servers, storage units, networking devices, etc. It refers to a virtualization environment where services enable the cloud platforms and applications to connect and operate. This is the data center(s) and the cost is often based on the resources used. IaaS delivers cloud computing services, typically in the form of a set of virtual machines with associated storage, processing capabilities, and other relevant services and network connectivity.
The deployment model for enables multiple applications, owned by different cloud consumers, to transparently share common underlying physical resources. This is a good alternative for companies instead of investing on their own stuff. The service layer model from bottom to top is IaaS, PaaS and SaaS. IaaS layer is at the bottom of the service model layer. The layer on top of IaaS is PaaS and it is common to build PaaS solutions on top of the IaaS environment to allow the platform to dynamically respond to demand by taking advantage of the IaaS functionality. Figure 1.3 illustrates the cloud service model layers.
Many researchers have attempted to define cloud frameworks by adding other essential components, such as management, quality, security and communication to the basic cloud structure IaaS, PaaS and SaaS. There is an overlap of cloud provision between the three layers, for example a component of information system platform as PaaS may be regarded as part of information system infrastructure as IaaS. Also SaaS may be considered as part of a software platform as PaaS.
Platform as a service (PaaS)
PaaS is considered as the complete cloud computing platform that provides provision and manages the cloud infrastructure. In addition, it provides deployment, development, and administration tools. Elasticity of the model is achieved by scaling up or down based on the system needs. The fault tolerance and the load balancing might be provided for the database management system to increase the reliability and enhance the performance. The Hardware as a service (HaaS) appears under the PaaS layer. Figure 1.4 illustrates the service model hierarchies. Pricing can be managed in this level on many dimensions to establish cloud platform, operating systems, database management systems, Web servers, programming language, etc.
PaaS is an abstract concept, unlike IaaS and SaaS. PaaS would be in the middle of the service layer model, with IaaS at the bottom and SaaS on the top to interface with the end users and consumers. What is being provided is part from the operating system and part from middleware. A proper PaaS provider takes care of everything needed to run some specific language or technology stack. PaaS provides a care free environment for developers to work, thus allow the developers to focus on coding and free from the configuration and maintenance of the underlying platform. By using PaaS, developers simply pick the languages and the required features, match those requirements with a provider that has them, and start coding. The support for Web development interfaces is available in PaaS, such as Simple Object Access Protocol (SOAP) or Representational State Transfer (REST). This allows the design and development of multiple Web services or mashup to reuse services or access databases.
Software as a service (SaaS)
Known as on-demand software, it provides the complete software solutions system, such as Customer relationship management (CRM), social networks, documentation management and content management. It is also a software delivery method to provide access to software and the corresponding functions remotely as a Web-based service. SaaS allows organizations to access business functionality at a cost typically less than paying for licensed applications. Software is hosted over cloud and users don’t need to invest in additional hardware. SaaS removes the need for organizations to handle the installation. Usually, the refer to the cloud most mean what is provided in SaaS. The services and their related data can be used combined or directly with SaaS providers. The benefits of using SaaS can be summarized as follows:
- Easier administration.
- Automatic updates and patch management at any time.
- Compatibility so that all users will have the same version of the software.
- Easier collaboration.
- Global accessibility.
SaaS services normally run behind a firewall on a network and provide on-demand usage. It is known as pay as you go paradigm, and customer will purchase functionality and pay for using it. Sometimes this service is available to general public totally free of charge. There is much more advantages for this approach include readily available, well tested functionality, ease of use, faster implementation, multi tenant efficiency, scalability, reliability and ease of management. SaaS is located at the top of the cloud service model and use the services provided by the lower layers. Figure 1.5 illustrates the cloud computing service relationships for IaaS, PaaS and SaaS.
SaaS offer benefits for both the users and the cloud computing providers. There is an effect of cloud computing for cloud providers and SaaS providers and cloud users. The top level can be recursive in which SaaS providers can also be SaaS users. For example a mashup provider of rental maps might be a user of the Craigslist and Google maps services.
Network as a service (NaaS)
After exploring the three main cloud services, here is a description for some other extra categories of cloud services, like NaaS, HaaS and DaaS. NaaS is considered to be part of the nomenclature of cloud computing. NaaS is based on describing the use of network connectivity services capability provided to the cloud service user. The optimization of resource allocations by network and computing resources is involved in NaaS. NaaS provides a cloud enabled pay as you go procurement model for network infrastructure and services and enables the network to be available as a subscription. This could be implemented in routers or cloud Virtual Private Network (VPN) gateways.
Traditional NaaS services include flexible and extended VPN and bandwidth on demand. Naas Service Model varies depending on the network enabler, the network user, and the service provided. Below is a description for the common models of NaaS :
- Virtual Private Network (VPN)
This model extends a private network and the resources contained in the network across public networks like the Internet. It enables a host computer to send and receive data across shared or public networks as if it were a private network with all the functionality and policies of the private network.
- Bandwidth on Demand (BoD)
Technique by which traffic bandwidth in an IT or telecom network is assigned based on requirements between different nodes or users. Under this model, the link bandwidth is dynamically adapted to the instantaneous traffic demands of the nodes connected to the link.
- Mobile Network Virtualization
Most common implementation of mobile virtual network is the Mobile Virtual Network Operator (MVNO), in which a mobile communication service provider does not own the radio spectrum or wireless network infrastructure over which the MVNO provides services to its customers.
Hardware as a service (HaaS)
Instead of purchase servers, software racks, and having to pay for the datacenter resources, the service provider rents those resources. Cloud provides application to customers using PaaS and SaaS, HaaS simply offers the hardware to the organization to utilize. With HaaS, it is possible to rent resources such as server space, memory, CPU cycles, storage space, or even network equipment. HaaS is considered as a service provision model for hardware based on the application resources needs. HaaS enables the dynamic scale up or down of the infrastructure and billing is based on the resources usage.
HaaS is considered as a sub category from PaaS as Figure 2.20 explained. PaaS provides the platform and the hardware which always available as a service through hosting providers. With dedicated hosting, the users still have to deal with dirty hardware issues like scalability, but using HaaS makes it a totally good experience. HaaS involves several pieces, such as:
- Service level agreements: an agreement between the provider and the client, guaranteeing a certain level of performance from the system,
- Computer hardware: These are the components whose resources will be rented out. Service providers often have this set up as a grid for easier scalability,
- Network: This includes hardware for firewalls, routers, load balancing, etc.,
- Internet connectivity: This allows clients to access the hardware from their own organizations,
- Platform virtualization environment: This allows the clients to run the virtual machines of their choice, and
- Utility computing billing: Typically set up to bill customers based on how many system resources are used.
Data as a services (DaaS)
DaaS is a sub category SaaS that is based on the concept that data can be provided on demand to the user regardless of the geographic or organizational separation of the provider and the consumer. The idea behind DaaS is to avoid the complexity and cost of running local database. Data provided as a service was at first primarily used in Web mashups, but now is being increasingly employed both commercially and less commonly within organizations. Most enterprises have used data stored in a self contained repository for which software was specifically developed to access and present the data in a human readable form. One result of this paradigm is the bundling of both the data and the software needed to interpret it into a single package, sold as a consumer product.
DaaS brings the notion that data quality can exist in a centralized place which is responsible for cleansing and enriching data and offering it to different systems, applications or users. Irrespective of where they were in the organization or on the network. As such, DaaS solutions provide the following advantages:
- Ease of use: There are no servers to provision and no redundant systems to worry about. The users are not worry about buying, installing, or maintaining hardware for the database,
- Power: The database isn’t housed locally, but that doesn’t mean that it is not functional and not effective. Depending on the vendor, the user can get custom data validation to ensure accurate information.
- Integration: The database can be integrated with other services to provide more value and power, for example, the user can tie the data in a database with calendars, email, and people to make the work more powerful, and
- Management: Because large databases benefit from constant pruning and optimization, this task need expensive resources to accomplish. With some DaaS offerings, this management can be provided as part of the service for much less expenses. The provider will often use offshore labor pools to take advantage of lower labor costs.
OneHoster is one of the best web hosting companies in Egypt, we offer many web hosting packages in Egypt and middle east like, cPanel storage hosting packages, cloud hosting, domain registration, dedicated servers solution, Email hosting, WordPress hosting, web hosting upgrades and hosting renewals to suit your requirements to host your website for small and medium sized businesses. OneHoster is also one of the top 10 website design companies, and top 10 digital marketing companies in Egypt and Middle east.
“OneHoster’s Team”